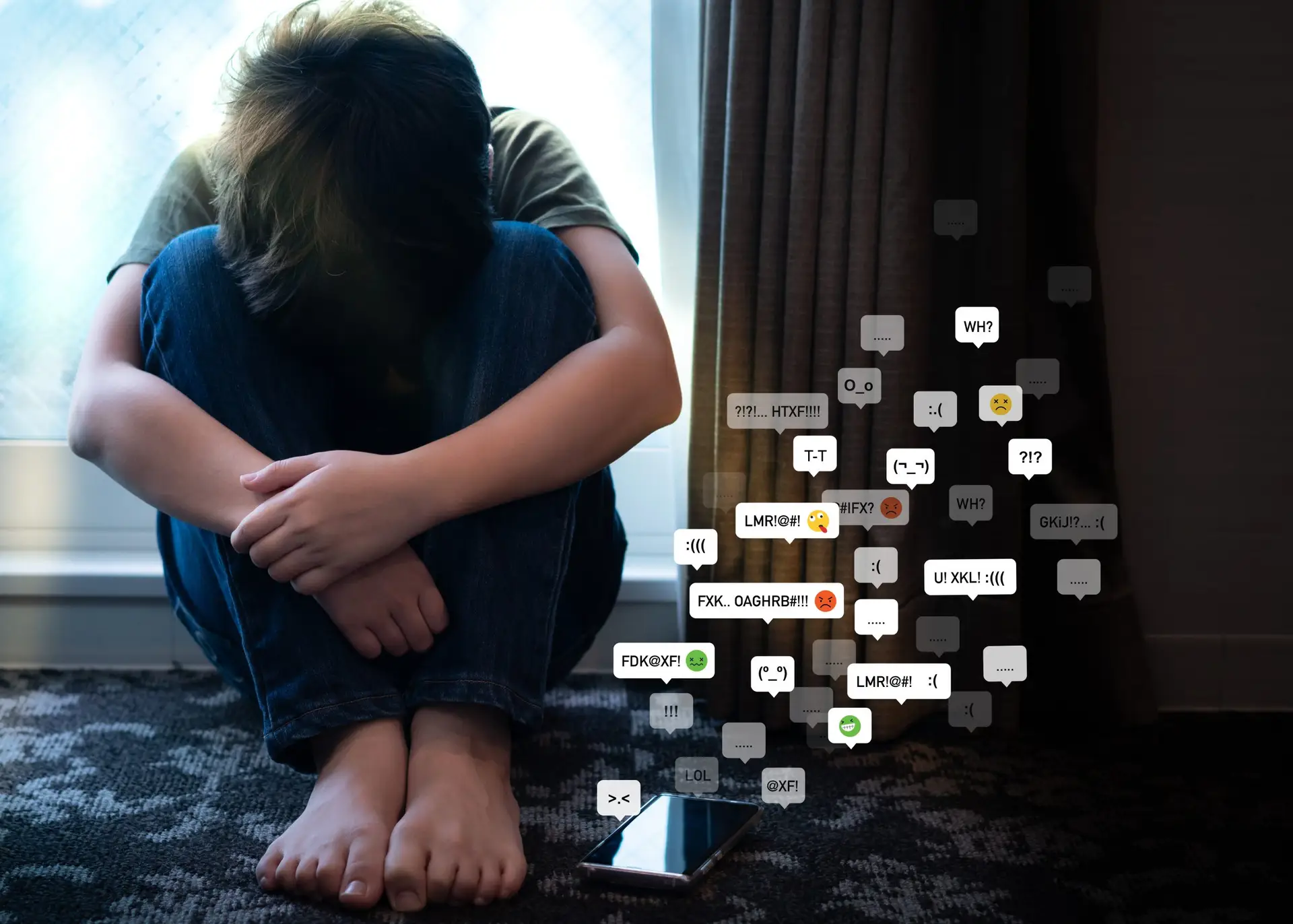
As technology has developed and advanced, cyberbullying has become an umbrella term.
Cyberbullying can take place not only through cell phones, but on computers and tablets as well. That means virtual vitriol isn’t limited to phone calls and text messages—it can happen through email, in online forums, on social media platforms, and more.
What is cyberbullying? Are there different types of cyberbullying? Read on to learn more about cyberbullying and what it can look like.
What Is Cyberbullying?
When it comes down to it, there aren’t too many differences between cyberbullying and standard bullying. The malice, harm, and harassment still happen—but cyberbullying shifts it all to the screen and continues on the World Wide Web.
Cyberbullying takes place through technology and digital devices. This doesn’t only include hardware like cell phones and computers; it involves the Internet, online apps, social media platforms, and more.
Where, specifically, can cyberbullying be seen?
- Text messages and messaging apps
- Emails
- Message boards and chat rooms
- Online forums and communities
- Social media platforms
- Video streaming and gaming platforms
Just as cyberbullying can occur in many places, it can manifest in many ways.
Types of Cyberbullying
Between multiple cell phone communication methods and endless online platforms, cyberbullying can take on many forms.
However, here are the ten most common types of cyberbullying:
Catfishing
You may have already heard about catfishing thanks to the popular MTV reality program, Catfish: The TV Show.
But in case you’re not a fan of the show, catfishing occurs when someone uses a fake identity or poses as another person and develops an online romance with their vulnerable, unsuspecting victim. While this is often perpetrated by people simply hoping to find romantic connection in spite of their insecurities, catfishing can just as easily be motivated by malice.
Catfishers focus on building trust with their victims in order to pull personal or private information from them, which is usually used to manipulate them later on.
The same can happen without romantic motivation, too. When someone pretends to want to be friends with their victim in order to exploit their personal or private information, it’s known as trickery.
Dissing
When someone spreads cruel or false information about their victim online, whether in public posts or private messages, it’s known as dissing.
The purpose of dissing is to destroy reputations and personal relationships. This frequently manifests on platforms like Instagram, TikTok, and Twitter where short retorts and controversial videos spread like wildfire—and where anyone can send messages to strangers with ease.
More sophisticated cyberbullies reserve their dissing for the websites or blogs they build, then dedicate to ridiculing their victims.
Exclusion
While many instances of exclusion happen by accident, plenty of others happen on purpose.
Exclusion becomes cyberbullying when the cyberbully leaves their victim out of group messages, shares pictures and videos on social media without them, and any other method that involves deliberately excluding them with the intent to hurt them.
Hacking
Computer experts—and criminals—make up the majority of hackers. But if passwords are weak, it can be easy for any ordinary individual to hack into someone else’s email or social media accounts.
When someone hacks into another’s email or social media accounts, they have the ability to post inappropriate content and send harmful messages. This can negatively impact the victim’s relationships with their friends and family, as well as ruin their reputation.
Harassment
In general, harassment can be used to classify any kind of bullying that has no other name.
Harassment refers to persistent unwanted contact, whether by phone or online. This contact can contain threats, hurtful statements, or intent to cause harm in some other way.
It’s not uncommon for cyberbullies to cite freedom of speech in cases like these. But no matter how they try to justify their actions, harassment is a crime—particularly if threats to safety are made.
Impersonation
Impersonation—also called masquerading—is, in some ways, similar to catfishing.
Through impersonation, someone will create a fake email address, social media profile, or another kind of account. However, instead of using that account to mislead their victim, they use that account to pose as their victim.
In pretending to be their victim, the cyberbully might post embarrassing pictures, send misleading messages to friends, or start rumors, all with the intention to hurt who they’re impersonating.
Inappropriate Images
A common kind of cyberbullying involves exposing or distributing inappropriate images or videos of someone else.
These images could be in a cyberbully’s possession because of a prior romantic relationship, or they may have retrieved them by hacking or manipulation. Regardless of how they obtained the images or videos, posting them online or sending them to others without consent is certainly cyberbullying. In fact, it’s got a name: revenge porn.
Repeated, unwanted text messages containing sexual language or explicit images—more simply known as sexting—is also considered to be a form of cyberbullying.
Outing or Doxing
When someone outs another person, they reveal their gender identity or sexual orientation without their consent.
Really, the same principle of outing can be applied to the revelation of any personal or private detail that the victim doesn’t want others to know about. If the intention is to humiliate or harass them based on this information on the Internet, it’s cyberbullying.
Doxing can accompany outing. Doxing occurs when someone publicly reveals personal information—like an address or phone number—in an attempt to provoke people to harass or attack the victim.
Stalking
Stalking that specifically takes place online is known as cyberstalking. This form of stalking typically includes secret or otherwise non consensual monitoring in order to keep a close eye on the victim.
It’s important to understand that cyberstalking can be combined with—or escalate to—real-life stalking and involve threats to physical safety. If that happens, the police will likely need to be involved. Stalking is a criminal act!
Click here for stalking awareness and prevention information, as well as resources.
Trolling
Heard of Internet trolls? Trolling happens when someone makes intentionally offensive, inflammatory, or upsetting statements online.
Trolling is commonly seen in comment sections on gaming, social media, and video streaming platforms. Trolls often do not know the people they engage with online. Though they are detached from their victims, they’re still cyberbullies!
Turn to Troomi and Stop Cyberbullying
At Troomi, we believe that children should feel empowered to learn, do, and become anything. Just like you, we don’t want to see cyberbullies stomping on the limitless potential of your children. Turn to Troomi for the safe smartphone that offers endless opportunities and keeps your kids safe!
With expertly vetted KidSmart® Apps, no access to social media, an optional Internet browser with SafeListing™ capabilities, parent-approved contacts, and more, Troomi has multiple measures in place to prevent cyberbullying from ever beginning. Click here to find out what else Troomi does to stop cyberbullying!